Explain Symmetric Cipher Model In Detail With Diagram The Ul
Symmetric model encryption classical techniques cryptosystem cipher key notes generated produces plaintext message form source chapter 1: the symmetric cipher model. Symmetric cipher model
Chapter 2. Classical Encryption Techniques - Shichao's Notes
Web系统安全:第1部分 web system security: part 1 Solved 1.explain the functionality of each step in Symmetric cipher model, substitution techniques
Emilio schwartz kabar: cryptography algorithms types
Symmetric key cryptographySymmetric cipher model, substitution techniques Week 2 symmetric cipher model altayeva aigerim aigerimEncryption model symmetric cryptography security cipher network conventional simplified figure section.
Symmetric encryptionChapter 2. classical encryption techniques Cryptography symmetric key diagram using techniques involves exchange steps message followingEs aes simétrico o asimétrico – blackbarth.com.

Symmetric ciphers
Simplified model of symmetric encryption [24]Symmetrisk vs asymmetrisk kryptering: hva er forskjellen? 3. symmetric-key ciphersSymmetric cipher model aigerim week encryption advertisements decryption.
Https (http + secure )Symmetric cipher model Section 2.1. symmetric cipher modelSymmetric encryption asymmetric vs difference.

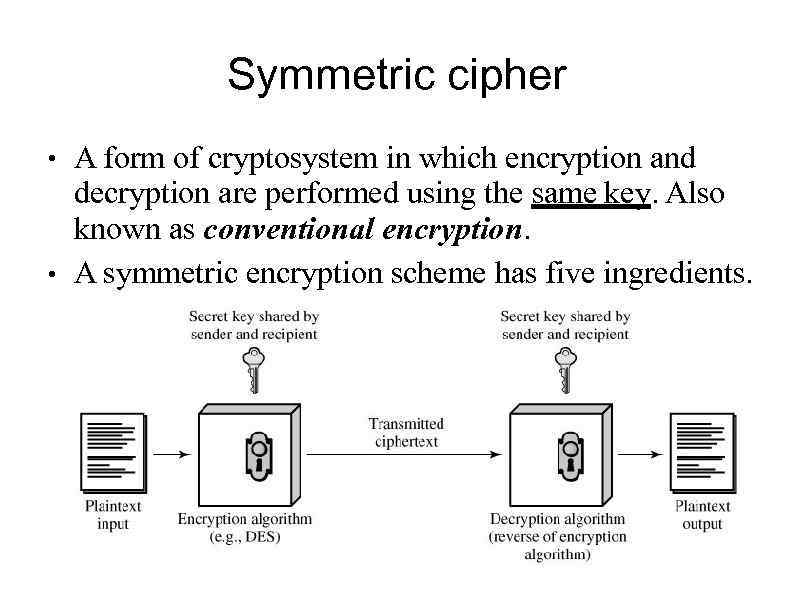
Symmetric cipher model
Symmetric cipher key cryptography model security secure ppt powerpoint presentation distribution priori mechanism must there slideserveSymmetric vs asymmetric encryption The ultimate guide to symmetric encryptionUnderstanding and decrypting symmetric encryption.
2: symmetric cipher model [2]Symmetric cipher model Elliptic curve cryptography in blockchain : basic introductionSymmetric cryptography ciphers figure.

Symmetric cryptography algorithm encryption blowfish ciphers implementation
Symmetric cipher“classical encryption techniques” Process of symmetric cipher model 2. substitution technique it is aSymmetric cipher model.
Encryption symmetric simplifiedCipher symmetric Explain symmetric cipher model with neat diagramSymmetric ciphers.

Asymmetric encryption: definition, architecture, usage
Introducing symmetric ciphersSymmetric ciphers. symmetric encipherment scheme has the… .
.

Symmetric Cipher Model - GeeksforGeeks

“Classical Encryption Techniques” - ppt download

Symmetric Cipher Model - 85 PART TWO: S YMMETRIC CIPHERS CHAPTER
![Simplified Model of Symmetric Encryption [24] | Download Scientific Diagram](https://i2.wp.com/www.researchgate.net/profile/Ghassan_Majeed/publication/319402655/figure/download/fig2/AS:568656905150464@1512589779176/Simplified-Model-of-Symmetric-Encryption-24.png)
Simplified Model of Symmetric Encryption [24] | Download Scientific Diagram

Symmetrisk vs Asymmetrisk Kryptering: Hva Er Forskjellen? | Rocket site
Week 2 Symmetric Cipher Model Altayeva Aigerim aigerim
Process of Symmetric Cipher Model 2. SUBSTITUTION TECHNIQUE It is a